 |
市場調查報告書
商品編碼
1433840
安全編排:市場佔有率分析、產業趨勢/統計、成長預測(2024-2029)Security Orchestration - Market Share Analysis, Industry Trends & Statistics, Growth Forecasts (2024 - 2029) |
||||||
※ 本網頁內容可能與最新版本有所差異。詳細情況請與我們聯繫。
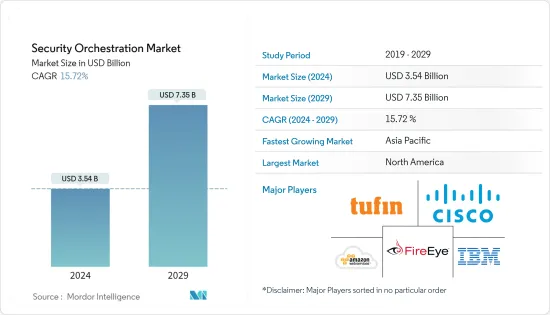
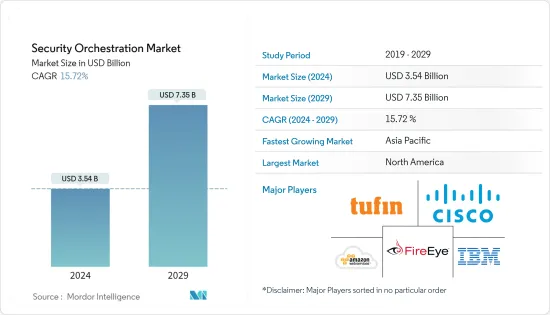
全球安全編排市場規模預計將在 2024 年達到 35.4 億美元,並在 2024-2029 年預測期內以 15.72% 的複合年成長率成長,到 2029 年將達到 73.5 億美元。
跨組織部署安全編排可以協助管理安全警報並防止嚴重的網路攻擊。隨著網路攻擊變得更加複雜,安全供應商正在開發更好的編配平台,以提供主動且全面的安全架構來處理關鍵業務應用程式。
主要亮點
- 影響中小企業的 BYOD 趨勢急劇增加,以及基於雲端的解決方案的快速部署和開發,導致安全漏洞和安全事件的增加,這加速了安全編排在各個組織中的採用。
- 隨著越來越多的公司採用安全編排平台來監控和管理電腦網路流量,網路取證的應用預計將增加並推動市場需求。
- 隨著連網型設備的普及以及各種 IT 服務和解決方案的日益採用,每天產生的資料量進一步增加,促使需要有效管理和遏制的潛在漏洞數量增加。範圍是巨大的。
- 這些解決方案還支援主動策略執行和審核合規性報告,包括 ITIL、PCI、健康保險流通和責任法案 (HIPAA)、薩班斯-奧克斯利法案 (SOX) 和 Gramm-Leach-Bliley 法案。遵守審核合規要求。這些因素正在推動市場成長。
主要市場趨勢
IT通訊產業預計將錄得顯著成長
- IT通訊業提供廣泛的全球和國內服務來連接數百萬客戶。這種多樣化的生態系統嚴重依賴基礎設施、網路和資料庫來執行其所有業務,因此經常容易受到網路攻擊。
- 電訊提供者通常儲存客戶的個人資訊,例如姓名、地址和財務資料。敏感資料是相關人員和網路犯罪分子竊取資金、勒索客戶或發動進一步攻擊的主要目標。這要求業界更多地關注現代解決方案、正確的工具、訓練有素的人員以及立即回應威脅的能力。
- SOAR 工具可協助 IT 團隊定義、標準化和自動化組織的事件回應活動。大多數 IT 組織使用這些工具來自動化保全行動和流程、回應事件以及管理漏洞和威脅。此外,安全編排還可以縮短參與企業安全的 IT 專業人員的威脅回應和解決時間。
- 透過雲端和物聯網增強資料連接已成為 IT 部門面臨的主要課題,而安全性已成為整個行業組織保護自己免受資料外洩的首要任務。此外,COVID-19大流行促使資訊和通訊技術公司重新考慮其業務流程,以便在整個疫情期間為客戶提供可靠的服務,特別是在通訊網路需求倍增的情況下,迫切需要提高網路效能。因此,企業正在採用這些安全編排解決方案來提高市場成長率。
北美佔最大市場佔有率
- 北美在安全編排市場上佔據主導地位,這要歸功於該地區許多著名的安全編排供應商,例如IBM公司、DXC科技公司、思科系統公司和FireEye公司。最終用戶產業的成長、政府在關鍵基礎設施上的支出、建立的研發中心以及對先進安全技術的需求等因素預計將推動該地區的市場成長。
- 該地區網路攻擊的增加進一步促進了市場的成長。 2021年,美國國家安全局(NSA)、網路安全和基礎設施安全局(CISA)、聯邦調查局(FBI)分別負責國防工業基地、緊急服務、食品和農業以及政府等16個機構。美國關鍵基礎設施部門。包括設施和資訊技術部門在內的14 個部門報告稱目睹了涉及勒索軟體的事件。
- 此外,組織承認網路複雜性在過去幾年中有所增加,並將在未來五年內繼續增加。這增加了對網路安全的需求,以防止駭客和網路攻擊保護產業流程,而這正是安全編排發揮作用的地方。
- 此外,該地區正在見證混合和多重雲端環境中採用的新雲端工具的爆炸性成長,而現有雲端平台也在不斷調整以適應新的混合實境。
競爭形勢
安全編排市場競爭非常激烈,有幾家主要公司進入該市場。從市場佔有率來看,目前該市場由少數大公司主導。此外,隨著雲端網路領域的出現,大多數公司都在增加在SOAR市場的佔有率,並在後續市場上開拓客戶。此外,公司正在選擇不同的策略,例如協作和解決方案推出,以促進市場成長率。
- 2023 年 3 月 - IBM 和 Cohesity 建立了新的合作夥伴關係,以滿足組織在混合雲端環境中提高資料安全性和可靠性的基本需求。 IBM Storage Defender 旨在透過單一視窗跨各種儲存平台使用 AI 和事件監控,以保護組織的資料層免受勒索軟體、人為錯誤和攻擊等威脅。
- 2023 年 2 月 - Morado Intelligence 是一家威脅情報公司,支援客戶對網路威脅情報和保全行動最佳化的需求;CyberFusion 為企業和 MSSP/MDR 提供低程式碼 SOAR 和威脅情報自動化 Cyware,為建置ISAC 和ISAO 的威脅情報共用解決方案已建立合作夥伴關係。此次合作的主要目標是使用 Cyware 的高級 TIP 和 SOAR 模組實現威脅資料的有效攝取、豐富、分析和回應,從而更輕鬆地滿足 Morado 強大的客戶組合需求。僅此而已。
其他福利:
- Excel 格式的市場預測 (ME) 表
- 3 個月分析師支持
目錄
第1章 簡介
- 調查先決條件
- 調查範圍
第2章調查方法
第3章執行摘要
第4章市場洞察
- 市場概況
- 產業吸引力-波特五力分析
- 新進入者的威脅
- 買家/消費者的議價能力
- 供應商的議價能力
- 替代品的威脅
- 競爭公司之間敵對關係的強度
- COVID-19 對市場的影響
第5章市場動態
- 市場促進因素
- 保全行動自動化以實現無縫工作流程的趨勢不斷增強
- 需要個人化的網路安全技術來解決網路複雜性
- 市場限制因素
- 專家缺乏認知
- 技術簡介
第6章市場區隔
- 類型
- 軟體
- 服務
- 最終用戶產業
- BFSI
- 資訊科技通訊
- 政府國防
- 電子商務
- 其他最終用戶產業
- 地區
- 北美洲
- 美國
- 加拿大
- 歐洲
- 英國
- 法國
- 德國
- 歐洲其他地區
- 亞太地區
- 中國
- 日本
- 澳洲
- 其他亞太地區
- 其他地區
- 拉丁美洲
- 中東/非洲
- 北美洲
第7章 競爭形勢
- 公司簡介
- IBM Corporation
- Tufin Software Technologies Ltd
- DXC Technology Company
- Cisco System Inc.
- Swimlane LLC
- RSA Security LLC
- FireEye Inc.
- DFLabs SpA
- Palo Alto Networks Inc.
- Siemplify Ltd
- Accenture PLC
- Amazon Web Services Inc.
- Cyberbit Ltd
- Forescout Technologies Inc.
第8章投資分析
第9章 市場機會及未來趨勢
The Security Orchestration Market size is estimated at USD 3.54 billion in 2024, and is expected to reach USD 7.35 billion by 2029, growing at a CAGR of 15.72% during the forecast period (2024-2029).
The implementation of security orchestration across various organizations can help manage security alerts and prevent severe cyber-attacks. As the sophistication level in cyber-attacks is increasing, security vendors are trying to develop better orchestration platforms to provide proactive and holistic security architecture to handle critical business applications.
Key Highlights
- An increase in the security breaches and occurrences due to dramatic growth in the BYOD trend affecting SMEs, along with the rapid deployment and development of cloud-based solutions, is fueling the application of security orchestration among various organizations.
- A rise in the application of network forensics is expected to drive the market demand, as a growing number of companies are adopting the security orchestration platform to monitor and manage their computer network traffic.
- Growing adoption of various IT enabled services and solutions, due to the growing popularity of connected devices, has further boosted the amount of data generated daily, subsequently resulting in a vast scope for potential vulnerabilities that need effective management and containment.
- Implementation of these solutions has also enabled improved adherence to audit and compliance requirements easily, with proactive policy enforcement and audit and compliance reports, such as ITIL, PCI, Health Insurance Portability and Accountability Act (HIPAA), Sarbanes-Oxley Act (SOX), and Gramm-Leach-Bliley Act. These factors have been aiding the growth of the market.
Key Market Trends
IT and Telecommunication Sector is Projected to Record Significant Growth
- The IT and telecommunication industry offers a wide range of global and domestic services for connecting millions of customers. This diverse ecosystem is more prone to frequent cyber attacks, as they are highly dependent on their infrastructure, network, and databases to perform any operation.
- Telecom organizations typically store customers' personal information, such as names, addresses, and financial data. Information-sensitive data is a compelling target for insiders or cyber-criminals to steal money, blackmail customers, or launch further attacks. Therefore, the industry demands a greater focus on updated solutions, the right tools, highly trained personnel, and the ability to respond to threats immediately.
- SOAR tools aid IT teams in defining, standardizing, and automating organizations' incident response activities. Most IT organizations use these tools to automate security operations and processes, respond to incidents, and manage vulnerabilities and threats. Moreover, security orchestration reduces the threat response and resolution time for IT professionals working in enterprise security.
- With the increased data connectivity with the cloud as well as IoT taking center stage in the IT sector, security has been a top priority for the all the organizations in the industry to protect themselves from the data breaches. Further, COVID-19 pandemic has led Information and communication technology organizations to rethink their business processes and improve their network performance to provide their customers with reliable services throughout the pandemic, specially when the demand for telecom networks has doubled. Thus, companies are adopting these security orchestration solutions thereby driving the market growth rate.
North America Accounts for the Largest Market Share
- North America dominates the security orchestration market, owing to many prominent security orchestration vendors across the region, such as IBM Corporation, DXC Technology Company, Cisco System Inc., FireEye Inc., etc. Factors such as the growing end-user industries, government expenditure toward critical infrastructure, well-established R&D centers, and the demand for advanced security technology across the region are expected to drive market growth.
- The growing number of cyber attacks in the region further contributes to the market growth. In 2021, The National Security Agency (NSA), the Cybersecurity and Infrastructure Security Agency (CISA), and the Federal Bureau of Investigation (FBI) reportedly witnessed occurrences involving ransomware against 14 of the 16 critical infrastructure sectors in the United States, including the Defense Industrial Base, Emergency Services, Food and Agriculture, Government Facilities, and Information Technology Sectors.
- Also, various organizations have admitted that network complexity has increased over the past few years and will continue to increase over the next five years. Therefore, there is a high need for network security to stop hacking and cyber-attacks from securing industrial processes, and that is where security orchestration plays its part.
- Further, the region is witnessing an explosion of new cloud tools adopted for hybrid and multicloud environments, while at the same time, established cloud platforms are pivoting to fit into the new hybrid reality.
Competitive Landscape
The security orchestration market is highly competitive and consists of several major players. In terms of market share, few major players currently dominate the market. Moreover, due to the emergence of the cloud network segment, most companies are increasing their SOAR market presence, tapping customers across the subsequent markets. Further, the players are opting for various strategies, such as collaborations and solution launches, thereby contributing to the market growth rate. For instance:
- March 2023-IBM and Cohesity have formed a new partnership to meet organizations' essential need for better data security and reliability in hybrid cloud settings. IBM Storage Defender is being developed to use AI and event monitoring across various storage platforms through one single window to assist in safeguarding organizations' data layer from threats, including ransomware, human error, and attack.
- February 2023-Morado Intelligence, a threat intelligence company that assists clients with their needs for cyber threat intelligence and security operations optimisation, and Cyware, a provider of the technology platform to build low-code SOAR and threat intel automation powered Cyber Fusion Centres for businesses and MSSPs/MDRs, as well as threat intelligence sharing solutions for ISACs and ISAOs, have formed a partnership. The partnership's primary objective is to make it easier for Morado's robust client portfolio to use Cyware's advanced TIP & SOAR modules to effectively ingest, enhance, analyze, and respond on threat data.
Additional Benefits:
- The market estimate (ME) sheet in Excel format
- 3 months of analyst support
TABLE OF CONTENTS
1 INTRODUCTION
- 1.1 Study Assumptions
- 1.2 Scope of the Study
2 RESEARCH METHODOLOGY
3 EXECUTIVE SUMMARY
4 MARKET INSIGHTS
- 4.1 Market Overview
- 4.2 Industry Attractiveness - Porter's Five Forces Analysis
- 4.2.1 Threat of New Entrants
- 4.2.2 Bargaining Power of Buyers/Consumers
- 4.2.3 Bargaining Power of Suppliers
- 4.2.4 Threat of Substitute Products
- 4.2.5 Intensity of Competitive Rivalry
- 4.3 Impact of COVID-19 on the market
5 Market Dynamics
- 5.1 Market Drivers
- 5.1.1 Rising Trend of Automated Security Operation for Seamless Workflow
- 5.1.2 Need of Disparate Cybersecurity Technologies to Handle Network Complexity
- 5.2 Market Restraints
- 5.2.1 Lack of Awareness among Professionals
- 5.3 Technology Snapshot
6 MARKET SEGMENTATION
- 6.1 Type
- 6.1.1 Software
- 6.1.2 Services
- 6.2 End-user Industry
- 6.2.1 BFSI
- 6.2.2 IT and Telecommunication
- 6.2.3 Government and Defence
- 6.2.4 E-commerce
- 6.2.5 Other End-user Industries
- 6.3 Geography
- 6.3.1 North America
- 6.3.1.1 United States
- 6.3.1.2 Canada
- 6.3.2 Europe
- 6.3.2.1 United Kingdom
- 6.3.2.2 France
- 6.3.2.3 Germany
- 6.3.2.4 Rest of Europe
- 6.3.3 Asia-Pacific
- 6.3.3.1 China
- 6.3.3.2 Japan
- 6.3.3.3 Australia
- 6.3.3.4 Rest of Asia-Pacific
- 6.3.4 Rest of the World
- 6.3.4.1 Latin America
- 6.3.4.2 Middle-East & Africa
- 6.3.1 North America
7 COMPETITIVE LANDSCAPE
- 7.1 Company Profiles
- 7.1.1 IBM Corporation
- 7.1.2 Tufin Software Technologies Ltd
- 7.1.3 DXC Technology Company
- 7.1.4 Cisco System Inc.
- 7.1.5 Swimlane LLC
- 7.1.6 RSA Security LLC
- 7.1.7 FireEye Inc.
- 7.1.8 DFLabs SpA
- 7.1.9 Palo Alto Networks Inc.
- 7.1.10 Siemplify Ltd
- 7.1.11 Accenture PLC
- 7.1.12 Amazon Web Services Inc.
- 7.1.13 Cyberbit Ltd
- 7.1.14 Forescout Technologies Inc.













